What is CryptoLocker?
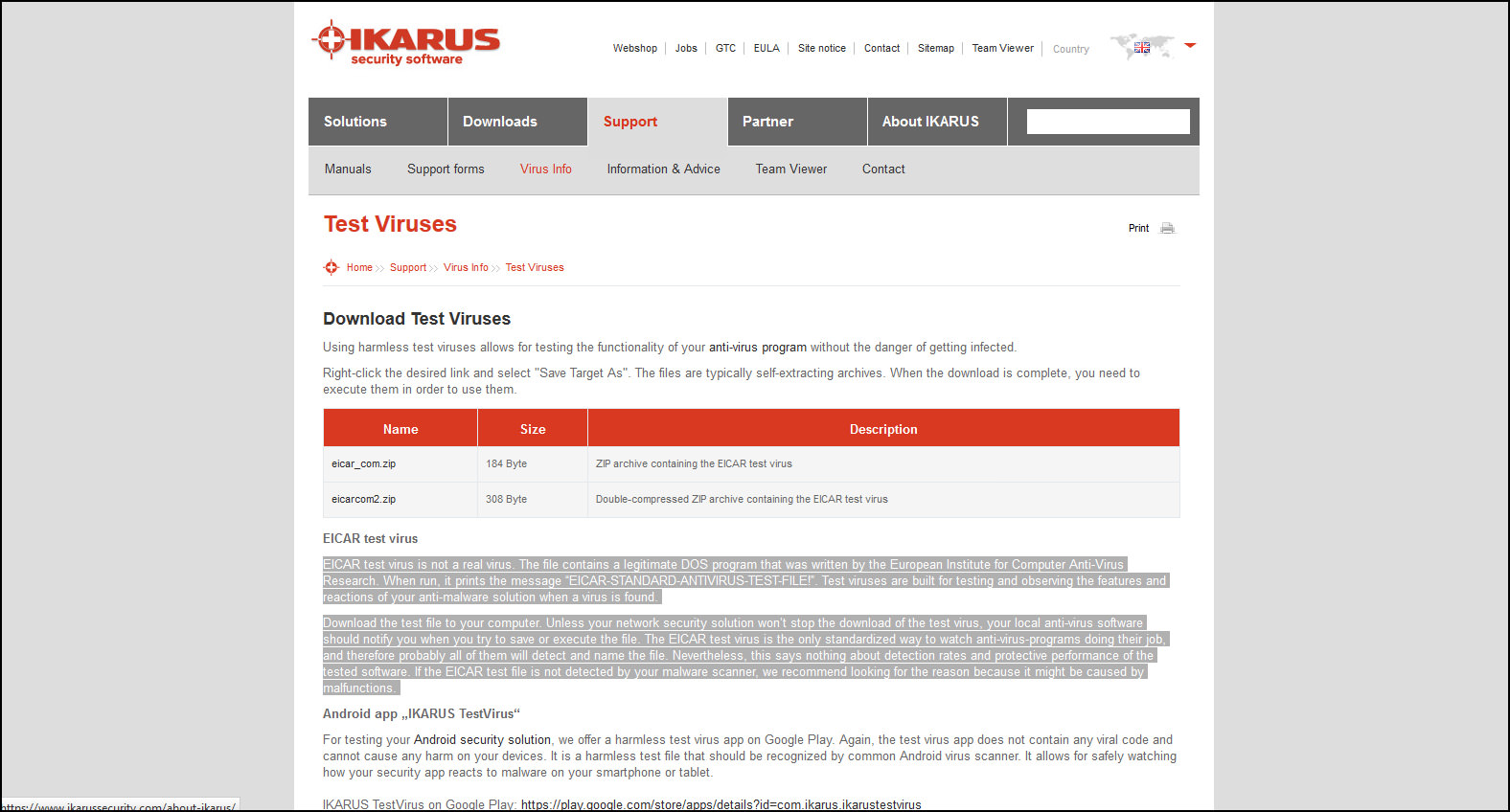
Apr 06, 2018 Download CryptoLocker for free. Lock and unlock your important files with an 8 character password. If you want to test software restriction policies, dump a copy of notepad.exe or something else benign into the prohibited locations and try to run it. If you want to check file watchers, make a script to make the files look like they have been attacked. If you want to check AV, use one of the AV test signature files. How can I get Cryptolocker on purpose (for testing) In short, I am looking to infect a few ESXi VMs to research how Cryptolocker infects individual workstations. We've had some bad luck with customers getting infected recently. Software restriction policies, and removing local admin rights seem to have no effect. Reasons for testing anti-virus software Obviously, there is considerable intellectual justification for testing anti-virus software against real viruses. If you are an anti-virus vendor, then you do this (or should do it!) before every release of your product, in order to ensure that it really works. Mar 02, 2021 Virus and Malware Samples: Includes APT, registration required; vx-underground; Yomi: Registration required; Be careful not to infect yourself when accessing and experimenting with malicious software. My other lists of online security resources outline Automated Malware Analysis Services and On-Line Tools for Malicious Website Lookups.
CryptoLocker is by now a well known piece of malware that can be especially damaging for any data-driven organization. Once the code has been executed, it encrypts files on desktops and network shares and “holds them for ransom”, prompting any user that tries to open the file to pay a fee to decrypt them. For this reason, CryptoLocker and its variants have come to be known as “ransomware.”
Malware like CryptoLocker can enter a protected network through many vectors, including email, file sharing sites, and downloads. New variants have successfully eluded anti-virus and firewall technologies, and it’s reasonable to expect that more will continue to emerge that are able to bypass preventative measures. In addition to limiting the scope of what an infected host can corrupt through buttressing access controls, detective and corrective controls are recommended as a next line of defense.
Get the Free Pen Testing Active Directory Environments EBook
FYI, this article is CryptoLocker specific. If you’re interested in reading about ransomware in general, we’ve written A Complete Guide To Ransomware that is very in-depth.
Update September 2018: Ransomware attacks have decreased significantly since their peak in 2017. CryptoLocker and it’s variants are no longer in wide distribution, and new ransomware has taken over. Ransomware has evolved as more of a targeted attack instead of the previous wide distribution model, and is still a threat to businesses and government entities.
What Does CryptoLocker Do?
On execution, CryptoLocker begins to scan mapped network drives that the host is connected to for folders and documents (see affected file-types), and renames and encrypts those that it has permission to modify, as determined by the credentials of the user who executes the code.
CryptoLocker uses an RSA 2048-bit key to encrypt the files, and renames the files by appending an extension, such as, .encrypted or .cryptolocker or .[7 random characters], depending on the variant. Finally, the malware creates a file in each affected directory linking to a web page with decryption instructions that require the user to make a payment (e.g. via bitcoin). Instruction file names are typically DECRYPT_INSTRUCTION.txt or DECRYPT_INSTRUCTIONS.html.
As new variants are uncovered, information will be added to the Varonis Connect discussion on Ransomware. For example, a variant known as “CTB-Locker” creates a single file in the directory where it first begins to encrypt files, named, !Decrypt-All-Files-[RANDOM 7 chars].TXT or !Decrypt-All-Files-[RANDOM 7 chars].BMP.
How to Prevent CryptoLocker
The more files a user account has access to, the more damage malware can inflict. Restricting access is therefore a prudent course of action, as it will limit the scope of what can be encrypted. In addition to offering a line of defense for malware, it will mitigate potential exposure to other attacks from both internal and external actors.
While getting to a least privilege model is not a quick fix, it’s possible to reduce exposure quickly by removing unnecessary global access groups from access control lists. Groups like “Everyone,” “Authenticated Users,” and “Domain Users,” when used on data containers (like folders and SharePoint sites) can expose entire hierarchies to all users in a company. In addition to being easy targets for theft or misuse, these exposed data sets are very likely to be damaged in a malware attack. On file servers, these folders are known as “open shares,” if both file system and sharing permissions are accessible via a global access group.
Download Cryptolocker Virus For Testing Sites
Although it’s easiest to use technologies designed to find and eliminate global access groups, it is possible to spot open shares by creating a user with no group memberships, and using that account’s credentials to “scan” the file sharing environment. For example, even basic net commands from a windows cmd shell can be used to enumerate and test shares for accessibility:
net view(enumerates nearby hosts)net view host(enumerates shares)net use X: hostshare(maps a drive to the share)dir /s(enumerates all the files readable by the user under the share)
These commands can be easily combined in a batch script to identify widely accessible folders and files. Remediating these without automation, unfortunately, can be a time-consuming and risky endeavor, as it’s easy to affect normal business activity if you’re not careful. If you uncover a large amount of accessible folders, consider an automated solution. Automated solutions can also help you go farther than eliminating global access, making it possible to achieve a true least-privilege model and eliminate manual, ineffective access-control management at the same time.
Download Cryptolocker Virus For Testing Free
How to Detect CryptoLocker
If file access activity is being monitored on affected files servers, these behaviors generate very large numbers of open, modify, and create events at a very rapid pace, and are fairly easy to spot with automation, providing a valuable detective control. For example, if a single user account modifies 100 files within a minute, it’s a good bet something automated is going on. Configure your monitoring solution to trigger an alert when this behavior is observed. Varonis DatAlert monitors and tracks file system behavior for ransomware attacks out-of-the-box. There is no need for extra configuration if Varonis is monitoring your data.
If you don’t have an automated solution to monitor file access activity, you may be forced to enable native auditing. Native auditing, unfortunately, taxes monitored systems and the output is difficult to decipher. Instead of attempting to enable and collect native audit logs on each system, prioritize particularly sensitive areas and consider setting up a file share honeypot.
A file share honeypot is an accessible file share that contains files that look normal or valuable, but in reality are fake. As no legitimate user activity should be associated with a honeypot file share, any activity observed should be scrutinized carefully. If you’re stuck with manual methods, you’ll need to enable native auditing to record access activity, and create a script to alert you when events are written to the security event log (e.g. using dumpel.exe).
If you’re PowerShell inclined, we’ve written a bit on how to combat CryptoLocker with PowerShell.
If your detective control mechanism can trigger an automated response, such as disabling the user account, the attack is effectively stopped before inflicting further damage. For example, a response to a user that generates more than 100 modify events within a minute might include:
Cryptolocker Virus Snopes
- Notifying IT and security administrators (include the affected username and machine)
- Checking the machine’s registry for known keys/values that CryptoLocker creates:
Get-Item HKCU:SoftwareCryptoLockerFiles).GetValueNames()
- if value exists, disable user automatically.
If recorded access activity is preserved and adequately searchable, it becomes invaluable in recovery efforts, as it provides a complete record of all affected files, user accounts, and (potentially) hosts. Varonis customers can use the output from report 1a (as described here) to restore files from a backup or shadow copy.
Depending on the variant of CryptoLocker, encryption may be reversible with a real-time disassembler.
Ransomware Safety Tips
- Update your antivirus and endpoint protection software – these solutions can help detect certain types of ransomware and prevent it from encrypting your files.
- Avoid phishing scams – phishing emails are the most prevalent delivery mechanism for ransomware.
- Keep backups of your documents – it’s much faster and easier to recover your documents from a backup than it is to decrypt them, if they’ve been compromised in a ransomware attack.
- Commit to a zero-trust/least privilege model – ransomware can only affect the folders a user can write to. A least privilege model limits that access to only what’s absolutely necessary.
- Monitor file activity and user behavior to detect, alert and respond to potential ransomware activity.
New ransomware variants are popping up all the time – luckily our dedicated security forensics team does the legwork for you and diligently updates the ransomware signatures that Varonis detects. See how it works with a free 1:1 demo and learn more about how our ransomware defense architecture is designed to protect enterprise data from zero-day attacks beyond the endpoint – catching ransomware that traditional perimeter security doesn’t see.
Ransomware is becoming a growing problem, posing a massive threat to all computer users – particularly businesses with many users and shared network drives.
The typical ransomware starts with a user being invited to “open” a document, but what they don’t realise that it is actually a program that silently starts encrypting every document the user has access to- even if they don’t have admin-rights on the computer. Once the files are encrypted the user offered the chance to decrypt the files for a fee.
RanSim is a free tool for Windows that will simulate several ransom-ware style attacks and will let you know how vulnerable your computer is. Providing you the opportunity to test various anti-virus tools.
It will ONLY simulate ransomware – it DOES NOT encrypt any files.
It tests vulnerability for:
- InsideCryptor – encrypts files using strong encryption and overwrites most of the content of the original files with the encrypted data.
- LockyVariant – simulates the behavior of a recent version of Locky ransomware.
- Mover – Encrypts files in a different folder using strong encryption and safely deletes the original files.
- Replacer – Replaces the content of the original files. A real ransomware would show a message that fools users into thinking they can recover them.
- Streamer – Encrypts files and writes data into a single file, using strong encryption, then deletes the original files.
- StrongCryptor – Encrypts files using strong encryption and safely deletes the original files.
- StrongCryptorFast – Encrypts files using strong encryption and deletes the original files.
- StrongCrytptorNet – Encrypts files using strong encryption and deletes the original files. It also simulates sending the encryption key to a server using an HTTP connection.
- ThorVariant – Simulates the behavior of a recent version of Thor ransomware.
- WeakCryptor – Encrypts files using weak encryption and deletes the original files.
DOWNLOAD: From the developer (requires personal information provided in a form) or from Major Geeks mirror.